In the world of telecommunications, bridging the gap between traditional mobile networks and modern internet-based voice systems is crucial for efficiency and cost savings. The GOIP (GSM over IP) gateway emerges as a pivotal piece of hardware in this landscape. It is a powerful tool for businesses but has also gained notoriety for its role in illicit activities. This article provides a comprehensive explanation of what a GOIP gateway is, its features, legitimate applications, and the risks associated with its misuse.

1. What is a GOIP Gateway?
A GOIP gateway is a hardware device that connects the Global System for Mobile Communications (GSM) network with Voice over Internet Protocol (VoIP) networks. In essence, it acts as a bridge, allowing voice calls and SMS messages to be seamlessly routed between the cellular world and the internet.
1.1. Core Concept: Bridging VoIP and GSM
Unlike a standard VoIP system that relies solely on an internet connection, a GOIP gateway is unique because it uses one or more SIM cards to connect directly to a mobile operator's network. This distinguishes it from traditional telephone systems that use fixed landlines (PSTN). As defined by manufacturers like DBL Technology and Hybertone, the device's primary function is to convert signals between the two distinct network types.
VoIP is a technology that allows voice transmission over IP networks, while GOIP is a specific hardware gateway that enables this technology to interface with GSM mobile networks.
1.2. ow It Works: A Technical Breakdown
The operational flow of a GOIP gateway is straightforward and can be divided into two main scenarios: outbound and inbound calls.
- Outbound Calls (VoIP to GSM): When a user on a VoIP system (e.g., an IP phone or a softphone on a computer) makes a call, the voice data travels over the internet to the GOIP gateway. The gateway receives this data, selects an available SIM card, converts the VoIP signal into a standard GSM signal, and dials the destination number through the mobile network. To the recipient, the call appears to originate from the local number of the SIM card.
- Inbound Calls (GSM to VoIP): When someone dials the number of a SIM card inserted into the GOIP gateway, the device receives the incoming GSM call. It then converts the voice signal into VoIP data packets and routes them over the internet to a pre-configured destination, such as an IP-PBX system, a specific IP phone, or a softphone application.
This dual-conversion capability allows businesses to integrate mobile communication lines directly into their corporate phone systems, creating a hybrid and highly flexible communication infrastructure.
2. Key Features and Technical Specifications
Modern GOIP gateways are equipped with a range of features that enhance their functionality, scalability, and management. These specifications are critical for businesses to evaluate when considering deployment.
2.1. Hardware and Connectivity
GOIP gateways are built with specialized hardware to handle call processing and network interfacing. A typical device includes:
- Processor and DSP: An ARM processor and a dedicated Digital Signal Processor (DSP) for voice encoding and decoding.
- SIM Card Slots: Available in various configurations, commonly with 4, 8, 16, or even 32 ports, allowing for multiple concurrent calls.
- Network Ports: At least one LAN port for internet connectivity and often a PC port for network sharing.
- Network Support: Compatibility with multiple GSM frequency bands (e.g., 850/900/1800/1900 MHz) is standard. Newer models increasingly support 3G and 4G/LTE networks to ensure better connectivity and voice quality as 2G/3G networks are phased out .
2.2. Protocol and Codec Support
To ensure seamless integration with existing VoIP infrastructure, GOIP gateways support a wide array of industry-standard protocols and codecs:
- VoIP Protocols: Full compatibility with SIP (Session Initiation Protocol) and H.323 is essential for connecting to IP-PBX systems (like Asterisk, 3CX), softswitches, and other VoIP platforms.
- Voice Codecs: Support for various codecs such as G.711 (A-law/μ-law), G.729A/B, and G.723.1 allows for balancing between voice quality and bandwidth consumption.
- Data and Control Protocols: They operate on a Linux-based OS and support a suite of network protocols including TCP/IP, HTTP (for web-based management), DHCP, DNS, and STUN for NAT traversal .
2.3. Advanced Management Capabilities
Beyond basic call routing, advanced GOIP gateways offer sophisticated features for optimization and large-scale management:
- Intelligent Call Routing: Also known as Least Cost Routing (LCR), this feature automatically selects the most cost-effective SIM card for an outbound call based on predefined rules like destination number, time of day, or carrier tariffs.
- Bulk SMS Functionality: Most gateways can send, receive, and forward SMS messages in bulk via an API or web interface, making them useful for marketing campaigns, appointment reminders, or two-factor authentication.
- Remote SIM Management (SIM Bank): For large or geographically distributed deployments, GOIPs can be paired with a "SIM Bank." This is a separate device that centralizes hundreds of SIM cards, which can then be remotely assigned to any GOIP gateway over the network. This drastically simplifies maintenance and SIM card rotation .
- IMEI Modification: A controversial feature that allows administrators to change the International Mobile Equipment Identity (IMEI) number of each channel. While it can be used to prevent carriers from blocking SIMs due to high usage, this feature is a primary enabler of illegal activities.
3. The Business Value: Legitimate Use Cases and Benefits
When used legally, GOIP gateways offer significant strategic advantages to businesses across various sectors by optimizing communication workflows and reducing operational costs.
3.1. Significant Cost Reduction
The most compelling benefit of a GOIP gateway is its ability to slash telecommunication expenses. By routing international or long-distance calls through a gateway equipped with a local SIM card in the destination country, businesses can convert expensive international calls into cheap local ones. This is particularly valuable for:
- Call Centers: Customer support and sales centers making a high volume of outbound calls can achieve massive savings.
- Multinational Corporations: Companies with offices in multiple countries can streamline inter-office communication without incurring international calling charges.
3.2. Enhanced Business Continuity and Reliability
In regions with unstable or unavailable broadband internet, a GOIP gateway serves as a crucial backup. Since it relies on the more ubiquitous GSM network, it can ensure that essential voice communication remains operational even during an internet outage. This makes it an ideal solution for businesses with field operations in remote areas, such as construction, agriculture, or energy sectors, where cellular coverage is often more reliable than wired internet .
3.3. Unified Communications and System Integration
GOIP gateways seamlessly integrate mobile lines into a company';s existing IP-PBX or Unified Communications (UC) platform. This integration allows mobile channels to be treated as part of the internal phone system, enabling features like call forwarding, conferencing, and allowing all employees to make outbound calls through a shared pool of SIM cards. This unifies fixed and mobile communication under a single, manageable system.
3.4. Applications Across Industries
The versatility of GOIP gateways makes them valuable in numerous industrial applications:
- Logistics and Fleet Management: Enables dispatchers to maintain constant, cost-effective contact with drivers, regardless of their location.
- Manufacturing: Supports automated voice alerts from machinery (via SCADA integration) and ensures redundant communication lines in large facilities.
- Remote Surveillance: Connects security systems like cameras and sensors to the GSM network, allowing for real-time alerts from unmanned sites without relying on internet connectivity.
- Oil and Gas: Provides a lifeline for crews in remote exploration sites, facilitating emergency response and operational updates where no other communication infrastructure exists.
4. The Dark Side: Misuse in Telecom Fraud
Despite its legitimate business applications, the very features that make GOIP gateways powerful—such as call origin masking and remote operation—have also made them a favorite tool for criminals engaged in telecommunications fraud.
4.1. How GOIP Enables Scams
Fraud syndicates exploit GOIP technology to deceive victims and evade law enforcement. The typical scam unfolds as follows:
- Remote Operation: Scammers, often located overseas, connect to a GOIP gateway via the internet.
- Local Placement: The gateway itself is physically located within the target country, equipped with multiple local SIM cards.
- Masked Calling: The scammer initiates a VoIP call that is routed to the gateway. The gateway then dials the victim's number using a local SIM card. As a result, the victim sees an incoming call from a familiar local number, which dramatically lowers their suspicion and increases the likelihood of them answering and falling for the scam.
Advanced techniques like "card-line separation," where the SIM cards are housed in a SIM bank at a different location from the dialing gateway, further complicate efforts by authorities to track and dismantle these fraudulent operations .
4.2. Regulatory Crackdown and Legal Risks
Governments worldwide are actively combating the misuse of GOIP devices. In China, for instance, the Anti-Telecom and Online Fraud Law explicitly prohibits the manufacturing, sale, or use of equipment that can alter caller IDs or illegally access public telecommunication networks. This legislation directly targets GOIP devices and similar "multi-card" hardware. Consequently, engaging in or facilitating such activities carries severe legal penalties.
For businesses, this means it is imperative to ensure that any use of GOIP technology is fully compliant with local laws and regulations to avoid inadvertently aiding criminal activities and facing legal repercussions.
5. The IP Gateway Market and Future Trends
The market for IP gateways, including specialized devices like GOIP, is driven by the global push for digital transformation and more efficient communication networks. As technology evolves, so too will the capabilities and role of GOIP gateways.
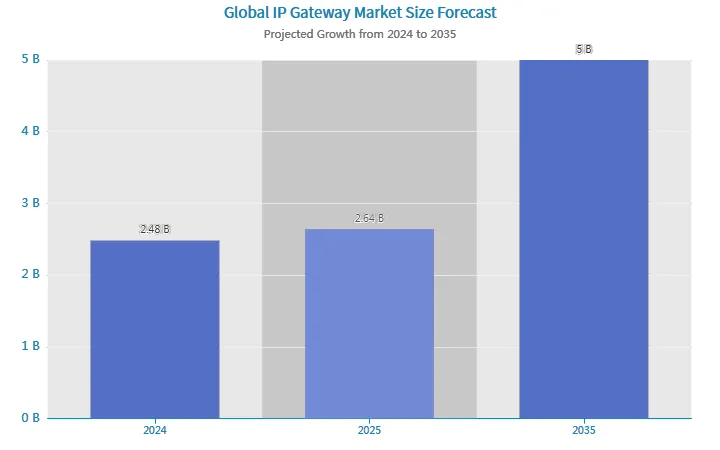
5.1. Market Size and Growth
The broader IP Gateway market is on a significant growth trajectory. According to a report by Wise Guy Reports, the market size was valued at $2.48 billion in 2024 and is projected to grow to $5 billion by 2035, with a compound annual growth rate (CAGR) of 6.6% between 2025 and 2035. This growth is fueled by increasing internet usage, the expansion of IoT, and the demand for secure and reliable network traffic management.
5.2. Key Technological Drivers
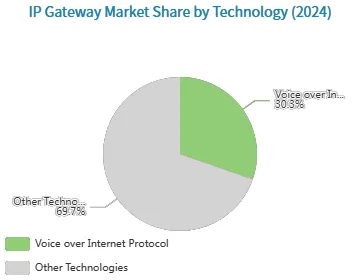
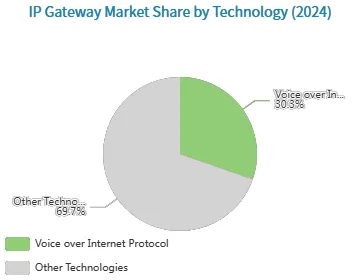
Within the IP gateway market, certain technologies are pivotal. A 2024 market share analysis highlights the dominance of established protocols. Voice over Internet Protocol (VoIP) remains a major component, underscoring the foundational role of technologies that convert and transmit voice over IP networks. The continued relevance of these protocols ensures a stable demand for gateway devices that can interface with them.
The market is driven by the need to integrate various communication standards. Session Initiation Protocol (SIP) is a cornerstone for initiating real-time sessions, while technologies like Network Function Virtualization (NFV) are enabling more agile and scalable network architectures. This technological landscape creates a fertile ground for advanced gateways that can manage diverse and complex traffic.
5.3. Future Outlook: 5G, AI, and Enhanced Security
The evolution of GOIP technology is expected to accelerate, influenced by several key trends:
- 5G Integration: Future GOIP gateways will incorporate 5G connectivity, offering significantly lower latency, higher bandwidth, and more reliable connections. This will enhance VoIP call quality and support more data-intensive applications .
- AI-Powered Enhancements: Artificial intelligence will be leveraged to optimize call routing, perform real-time analysis of call data, and proactively detect fraudulent patterns. A GSMA report notes that operators like China Unicom are already using AI-driven systems for anti-fraud purposes .
- Enhanced Security: In response to widespread misuse, manufacturers will face increasing pressure to integrate more robust security features, including stronger encryption, multi-factor authentication, and advanced fraud detection algorithms.
- Deeper Cloud Integration: GOIP gateways will become more tightly integrated with cloud-based Unified Communications as a Service (UCaaS) platforms, offering businesses more flexible and scalable deployment models.
6. Choosing and Securing a GOIP Gateway: Best Practices
For businesses considering a GOIP gateway, making the right choice and implementing strong security measures are paramount to maximizing benefits while minimizing risks.
6.1. Selecting the Right Gateway for Your Needs
A thorough assessment of your organization's communication requirements is the first step. Key factors to consider include:
- Channel Capacity: Choose a model (4, 8, 16, or 32-port) based on your peak concurrent call volume. Under-provisioning can lead to dropped calls and poor quality.
- Network Compatibility: Ensure the device supports the cellular network standards (3G, 4G/LTE) and frequency bands used in your regions of operation.
- PBX Integration: Verify compatibility with your existing IP-PBX system, including support for SIP trunking and necessary codecs.
- Scalability: Select a model that allows for future expansion, either through daisy-chaining or centralized management systems like SIM Banks.
- Management Interface: A user-friendly web GUI is crucial for easy configuration, monitoring, and troubleshooting.
6.2. Essential Security Measures
Securing your GOIP gateway is not optional—it is a critical responsibility. Many devices have been found to have significant vulnerabilities, such as weak default credentials, unauthenticated access to sensitive information, and cross-site scripting (XSS) flaws . To protect your device from unauthorized access, follow these best practices:
- Change Default Credentials: Immediately change all default administrator passwords upon installation.
- Implement Access Control: Use strong, unique passwords and configure trust lists to restrict access to authorized IP addresses only.
- Use Firewalls and VLANs: Isolate the gateway on your network using a firewall and Virtual LANs (VLANs) to protect it from both external and internal threats.
- Keep Firmware Updated: Regularly check the manufacturer's website for firmware updates, which often contain critical security patches.
- Disable Unnecessary Services: Turn off any unused features or ports to reduce the attack surface.
- Monitor and Audit Logs: Regularly review access and activity logs to detect any suspicious behavior.
7. Conclusion: A Double-Edged Sword
The GOIP gateway is a quintessential example of a technology that is a double-edged sword. On one hand, it offers legitimate businesses a powerful tool to reduce communication costs, enhance reliability, and create a unified, flexible telephony system. Its value in industries from logistics to manufacturing is undeniable.
On the other hand, its capacity for anonymity and remote operation has made it an indispensable asset for criminals, facilitating widespread telecommunications fraud that causes significant financial and emotional harm. This has rightly drawn the attention of regulators and law enforcement agencies globally.
For any organization, the path forward requires a cautious and responsible approach. Leveraging a GOIP gateway for its business benefits is viable only when done within the strict confines of the law and with robust security measures in place. As the technology continues to evolve with the integration of 5G and AI, the challenge will be to harness its power for good while collaboratively building stronger defenses against its misuse.

 English
English Deutsch
Deutsch 한국어
한국어 Русский
Русский Français
Français 日本語
日本語 لالعربية
لالعربية हिन्दी
हिन्दी Español
Español Português
Português 繁体中文
繁体中文 简体中文
简体中文