Recently, Indian authorities, including the Central Bureau of Investigation (CBI), have launched a major investigation into an illegal Voice over Internet Protocol (VoIP) exchange that was uncovered in Bihar. This is not just a routine telecom violation — the VoIP setup is allegedly tied to large-scale cybercrime activities, including frauds that exploit weak telecom systems and deceive the public.
In simple terms, this case revolves around an unauthorized telecommunications operation that illegally used VoIP technology and a device called a SIM box to reroute international calls into India through local phone networks. The result was a way for fraudsters to mask the origin of their calls and potentially use them for criminal purposes, causing financial loss to telecom operators, loss of government revenue, and risks to public safety.
To understand why this is a big deal, we need to explore several things:
- What a VoIP exchange is and how it works
- Why an illegal VoIP exchange is harmful
- How fraudsters use this technology for scams
- Why the CBI is investigating this case and what investigators have found so far
- How this fits into the broader landscape of cyber-enabled telecom fraud in India
1. What Is VoIP and a VoIP Exchange?
Voice over Internet Protocol (VoIP) is a technology that allows people to make voice calls using the internet instead of traditional phone networks. Services like Skype, WhatsApp calls, Zoom, Telegram calls, and many international call services use VoIP because it’s cheaper, flexible, and can work on any internet connection.
A VoIP exchange is a system that routes phone calls using internet protocols. In legitimate telecom systems, VoIP exchanges are used by telecom companies or service providers to connect calls over long distances while minimizing cost. When done legally and regulated properly, this helps reduce calling charges and makes communication more efficient.
However, when VoIP technology is misused, criminals can exploit it to bypass legitimate network controls, hide call origins, and evade international calling charges. That’s what’s allegedly happening in the case now under investigation: an illegal VoIP exchange that’s not authorized by telecom regulators.
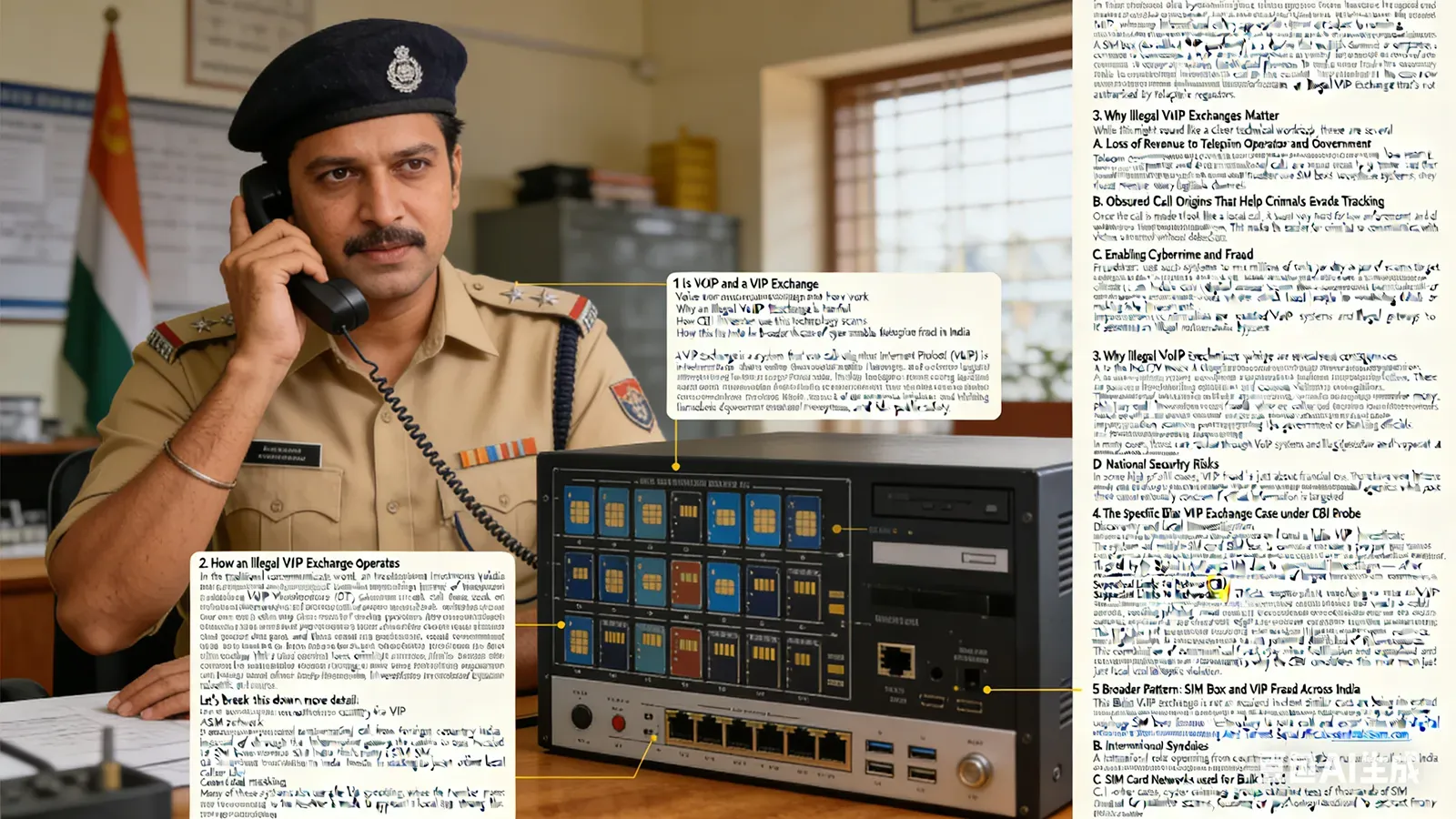
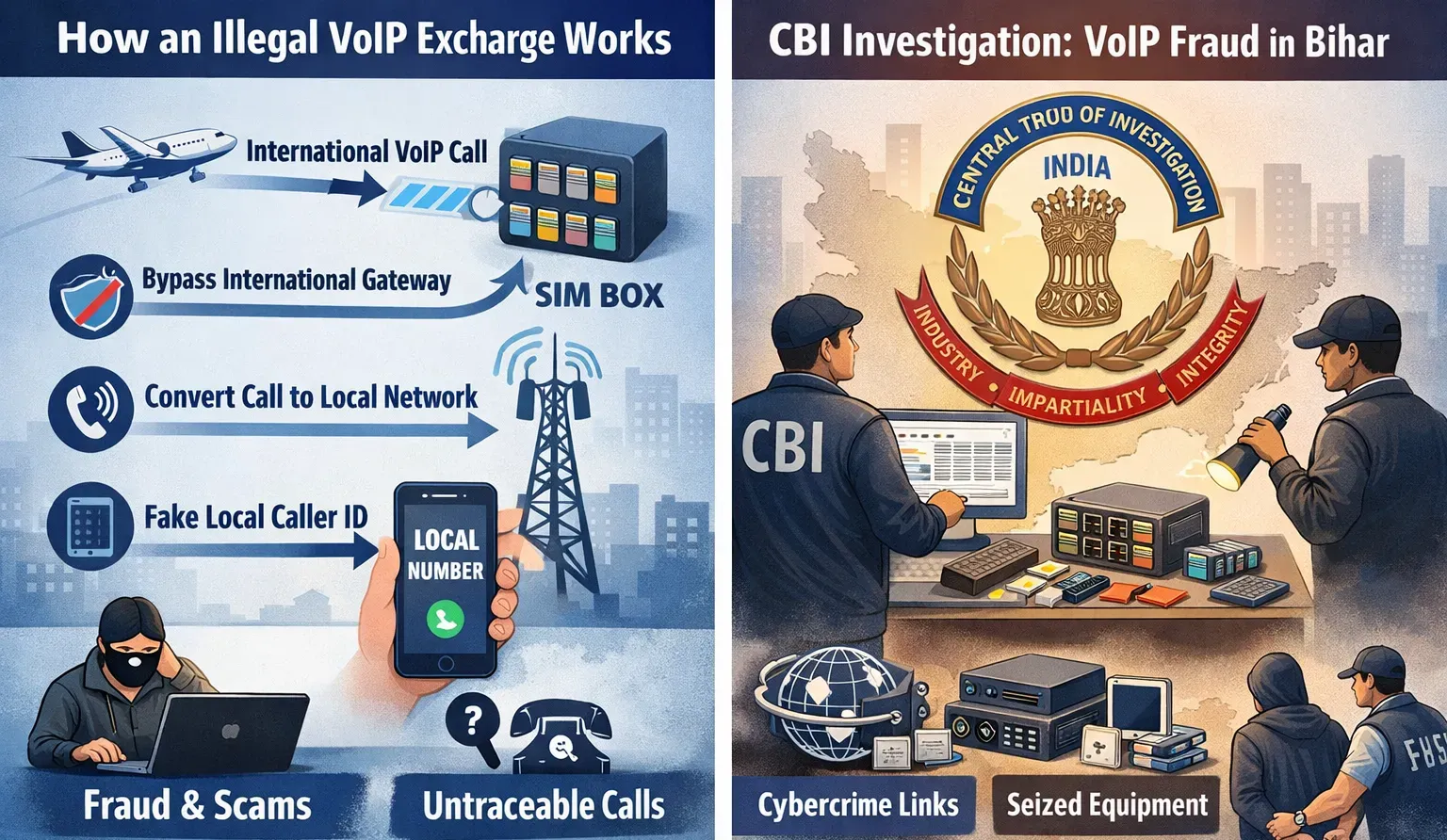
2. How an Illegal VoIP Exchange Operates
In the traditional telecommunications world, an international call from a foreign country to India should pass through licensed international gateways. These are regulated by authorities such as the Department of Telecommunications (DoT), which ensures that international calls pay appropriate tariffs and are subject to monitoring.
A SIM box (also called a VoIP gateway) is a device that contains multiple SIM cards from a mobile operator. It connects a VoIP call (internet-based) to a traditional mobile network by pretending to be many individual mobile phones. This setup allows voice traffic from outside the country to be rerouted into local networks as if it were domestic calls, hiding the original source and avoiding regulated international call routes.
Let’s break this down in more detail:
- International VoIP call arrives: A call originates from another country via a VoIP network.
- SIM box intercepts the call: Instead of going through the proper international gateway, the call is routed to a SIM box located locally in India that has many active SIM cards.
- Call appears local: The SIM box forwards the call into the domestic mobile network using one of its SIM cards, making it look like just an ordinary local call.
- Caller ID masking: Many of these systems also use caller ID spoofing, where the number presented to the receiver is made to appear local even though the call actually came from abroad.
This entire process lets criminals bypass telecom monitoring systems, avoid international tariffs, and cloak the real source of the call. It’s essentially an illegal telecommunications bypass.
3. Why Illegal VoIP Exchanges Matter
While this might sound like a clever technical workaround, there are several serious consequences:
A. Loss of Revenue to Telecom Operators and Government
Telecom companies and governments lose money because international calls are supposed to pay tariffs and fees that fund network infrastructure and regulation. When fraudsters use SIM boxes to bypass these systems, they divert revenue away from legitimate channels.
B. Obscured Call Origins That Help Criminals Evade Tracking
Once the call is made to look like a local call, it becomes very hard for law enforcement and telecom regulators to trace where it originally came from. This makes it easier for criminals to communicate with victims without detection.
C. Enabling Cybercrime and Fraud
Fraudsters use such systems to make millions of calls per day as part of scams that target unsuspecting citizens. These can include:
- Digital arrest scams where scammers pretend to be law-enforcement officers and coerce victims into transferring money.
- Phishing and investment frauds where callers trick people into revealing banking details or making fake investments.
- Impersonation scams pretending to be government or banking officials.
In many cases, these calls are routed through VoIP systems and illegal gateways to avoid detection and to operate at scale.
D. National Security Risks
In some high-profile cases, VoIP fraud isn’t just about financial loss. There have been instances where scammers made calls pretending to be from defence or national agencies, which poses a national security concern if critical information is targeted.
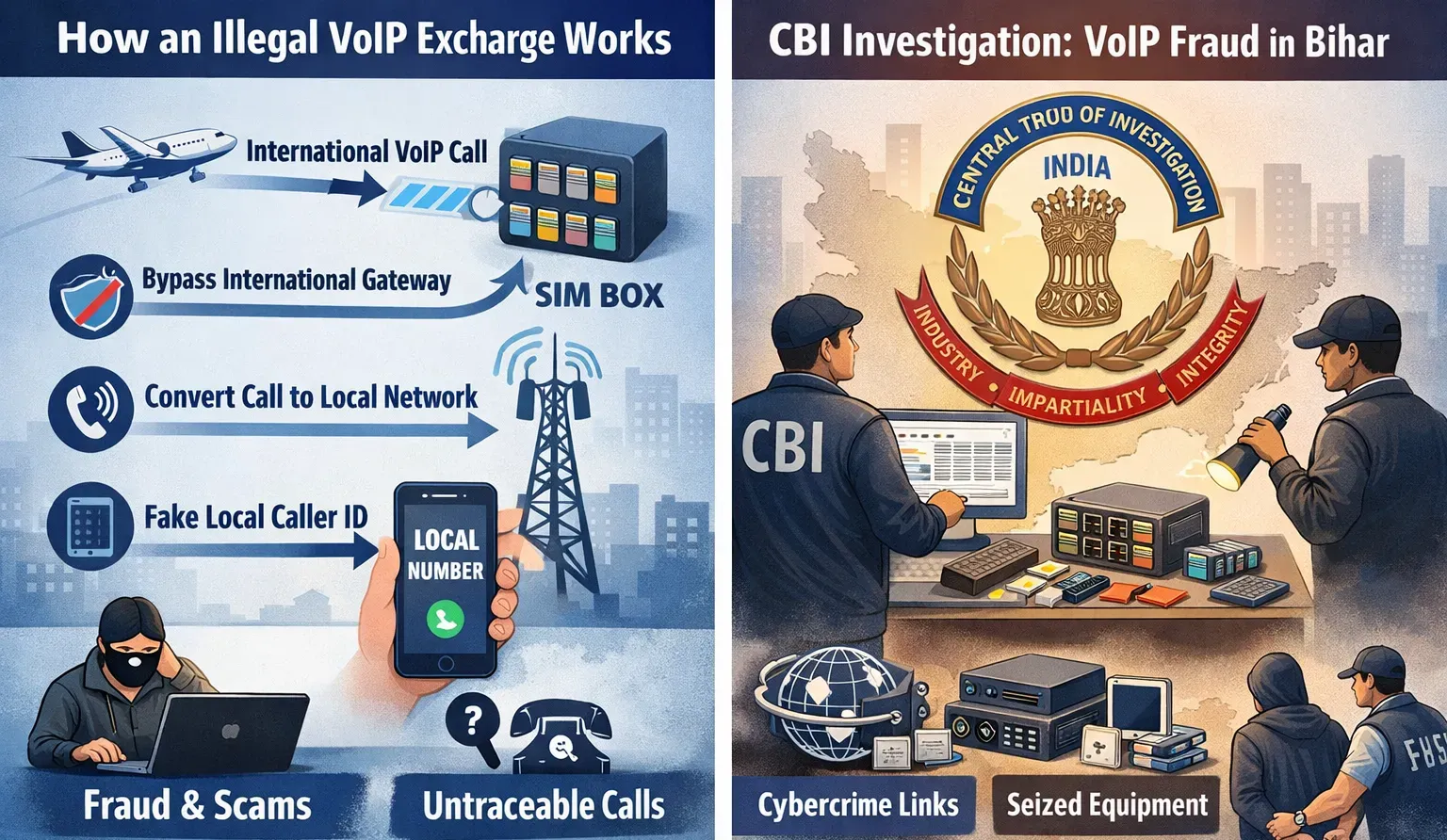
4. The Specific Bihar VoIP Exchange Case Under CBI Probe
According to the IndiaTV News article and supporting reports:
Discovery and Local Investigation
-
In Bhojpur district, Bihar, local police discovered an illegal VoIP exchange.
-
The system used multiple SIM cards and SIM boxes to convert international calls into local calls without proper authorization.
-
It was flagged by the Digital Intelligence Unit due to unusual patterns of call traffic and potential misuse.
Shift to Central Bureau of Investigation (CBI)
-
The case was initially registered by Bihar police, but because of the severity and suspected cybercrime links, it was transferred to the Central Bureau of Investigation — India’s premier federal investigative agency — after a government notification.
-
The CBI’s involvement indicates concerns that the VoIP exchange was more than a local scam; it may be part of larger transnational cybercrime networks.
Suspected Links to Fraud Networks
-
Officials suspect that the illegal VoIP setup was being used to aid large-scale cybercrimes, possibly including phishing, fraud, and socially engineered extortion schemes.
-
Investigators believe that fraudsters used the exchange to mask call origin and coordinate scam operations across regions.
Telecom Cards and Distribution
-
The investigation has reportedly traced some of the SIM cards used in this system back to fraudulent procurements through point-of-sale operators in other parts of the country.
-
This highlights not just technology misuse, but also potentially illegal distribution of telecom resources.
This combination of telecom fraud, cybercrime facilitation, and organized wrongdoing is why the CBI considers this more than just a local telecom violation.
5. Broader Pattern: SIM Box and VoIP Fraud Across India
This Bihar VoIP exchange is not an isolated incident. Similar cases are being investigated nationwide, showing a persistent pattern of telecom and cyber fraud involving VoIP technology and SIM boxes. Examples from recent reports include:
A. Large SIM Box Networks Across Cities
Police in Delhi busted syndicates using SIM box technology to route calls and extort victims with “digital arrest” scams by impersonating Anti-Terrorist Squad officials. (sentinelassam.com)
B. International Syndicates
A transnational crew operating from countries like Cambodia rerouted calls into India for punitive scams, focusing on psychological coercion to extract money from victims.
C. SIM Card Networks Used for Bulk Fraud
In other cases, cybercriminal groups obtained tens of thousands of SIM cards fraudulently to send bulk messages for scams such as phishing or fake investment offers — often routed through illegal telecom gateways.
D. Unlawful Gateways Bypassing Telecom Infrastructure
In other states like UP and Karnataka, police have uncovered illegal gateways providing unmonitored access for international calls disguised as local calls. (ThePrint)
E. National Efforts to Counter Scams
Regulatory bodies like the Telecom Regulatory Authority of India (TRAI) have also mandated numbered series changes (such as “1600” numbers) to make official calls easier to recognize and reduce scam incidents. (商业标准)
Together, these incidents show that VoIP and SIM box fraud isn’t a niche problem — it’s a national telecom and cybercrime issue with both financial and security implications.
6. Why This Investigation Matters
There are several reasons why the CBI’s probe into the illegal VoIP exchange is significant:
A. Protecting Citizens
VoIP-enhanced scams like “digital arrest” and phishing have drained billions of rupees from victims and caused psychological distress. Strong enforcement helps deter scammers.
B. Securing Telecom Infrastructure
Telecom networks are critical to national infrastructure. Illegal gateways undermine regulations, hurt telecom operators financially, and weaken the integrity of communication networks.
C. International Crime Networks
The cross-border nature of many SIM box operations suggests coordination with international criminal groups. Investigating these helps build better mechanisms for global cooperation.
D. Strengthening Legal Enforcement
The escalating involvement of the CBI reflects a broader recognition that cybercrime and telecom fraud require specialized expertise and federal authority to investigate comprehensively.
7. How Illegal VoIP Schemes Facilitate Scams
To appreciate how this telecom fraud works in practice, it helps to understand the common scams that benefit from illegal VoIP exchanges:
A. Digital Arrest Scams
In this scheme, callers impersonate law enforcement or government agencies, allege that the victim is involved in a crime, and coerce them into transferring money to “resolve” the issue. These calls often use VoIP systems to spoof local numbers and evade tracking.
B. Phishing and Investment Fraud
Scammers call hundreds or thousands of people via VoIP-enabled networks to promote fake loans, investments, or financial services, collecting personal and banking information.
C. Bank and Authority Impersonation
Cybercriminals often claim to be from banks, telecom regulators (like TRAI), or financial authorities to trick people into sharing OTPs or sensitive login credentials, which are then used for theft. (商业标准)
D. Bulk SMS and Phishing
Some networks don’t just make calls — they send millions of bulk SMS that are used in coordinated phishing campaigns. These messages frequently link back to VoIP call networks for follow-up contact.
In all of these scams, illegal VoIP exchanges help criminals operate at scale and avoid detection by routing traffic through unauthorized gateways.
8. Enforcement and Next Steps
The CBI’s probe is likely to involve multiple investigative techniques:
- Tracing call traffic and SIM usage patterns
- Interviews with telecom personnel and SIM card distributors
- Coordination with agencies such as DoT, TRAI, and international law enforcement
- Seizure of equipment, servers, SIM boxes, and digital evidence
Broadly, this crackdown is part of a larger trend where Indian authorities are taking cybercrime and telecom fraud seriously, stepping up prosecutions, and trying to shut down entire networks rather than individual actors.
Conclusion
The illegal VoIP exchange now under CBI investigation is not just a technical telecom violation — it’s a complex criminal infrastructure that enabled large-scale fraud, disguised call origins, and undermined regulatory safeguards. Because of the way VoIP technology was manipulated, fraudsters could mask their activities, evade detection, and conduct mass-targeted scams that financially and psychologically harmed thousands of victims.
India’s enforcement agencies, including the CBI, are now trying to dismantle this network, gather evidence, and hold accountable those responsible — including potential links to larger international cybercrime syndicates that have exploited the loopholes in telecom systems.
If you’d like an even deeper look into how VoIP fraud technology works or what legal penalties apply in India for these offenses, just let me know!

 English
English Deutsch
Deutsch 한국어
한국어 Русский
Русский Français
Français 日本語
日本語 لالعربية
لالعربية हिन्दी
हिन्दी Español
Español Português
Português 繁体中文
繁体中文 简体中文
简体中文