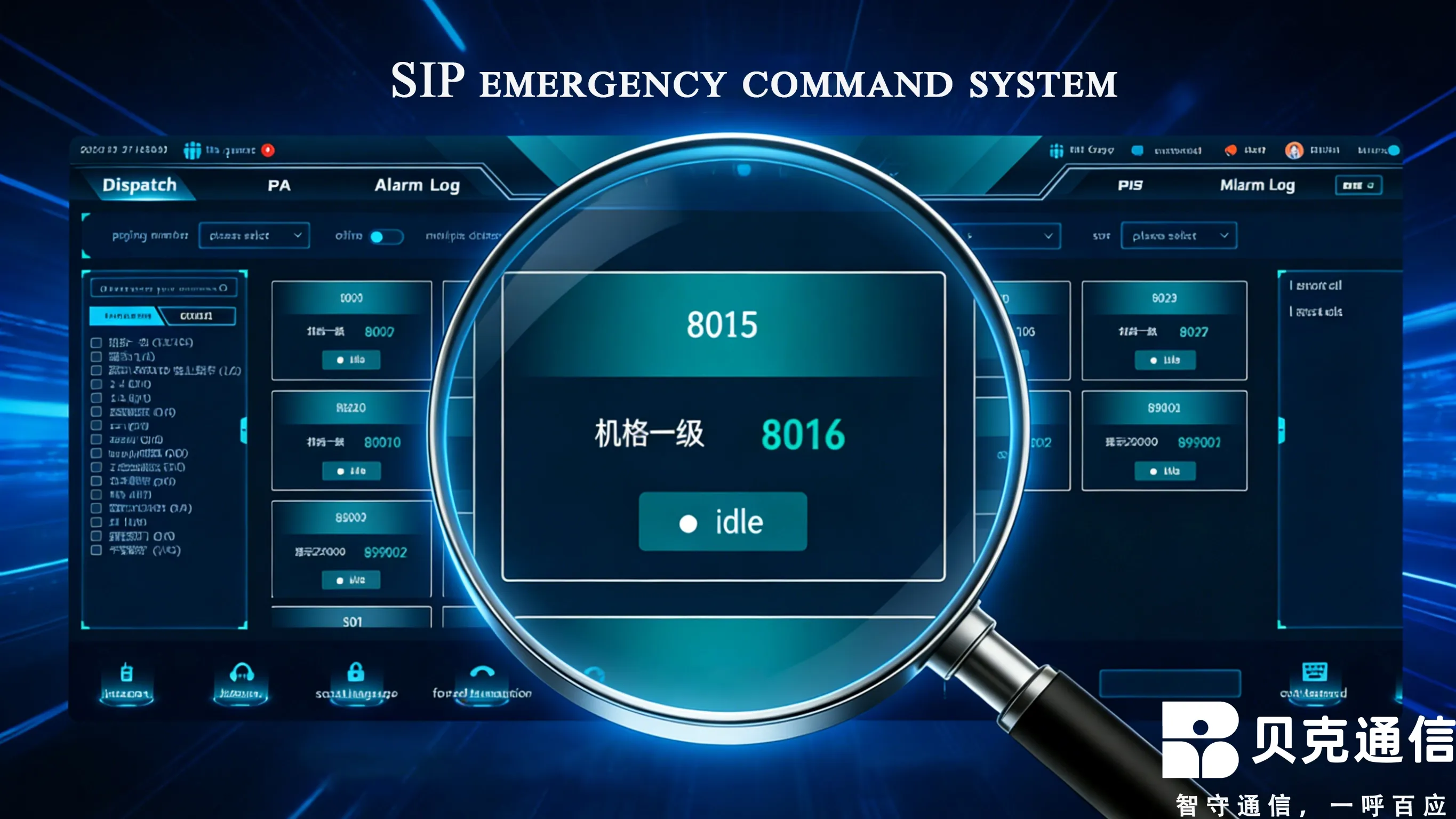
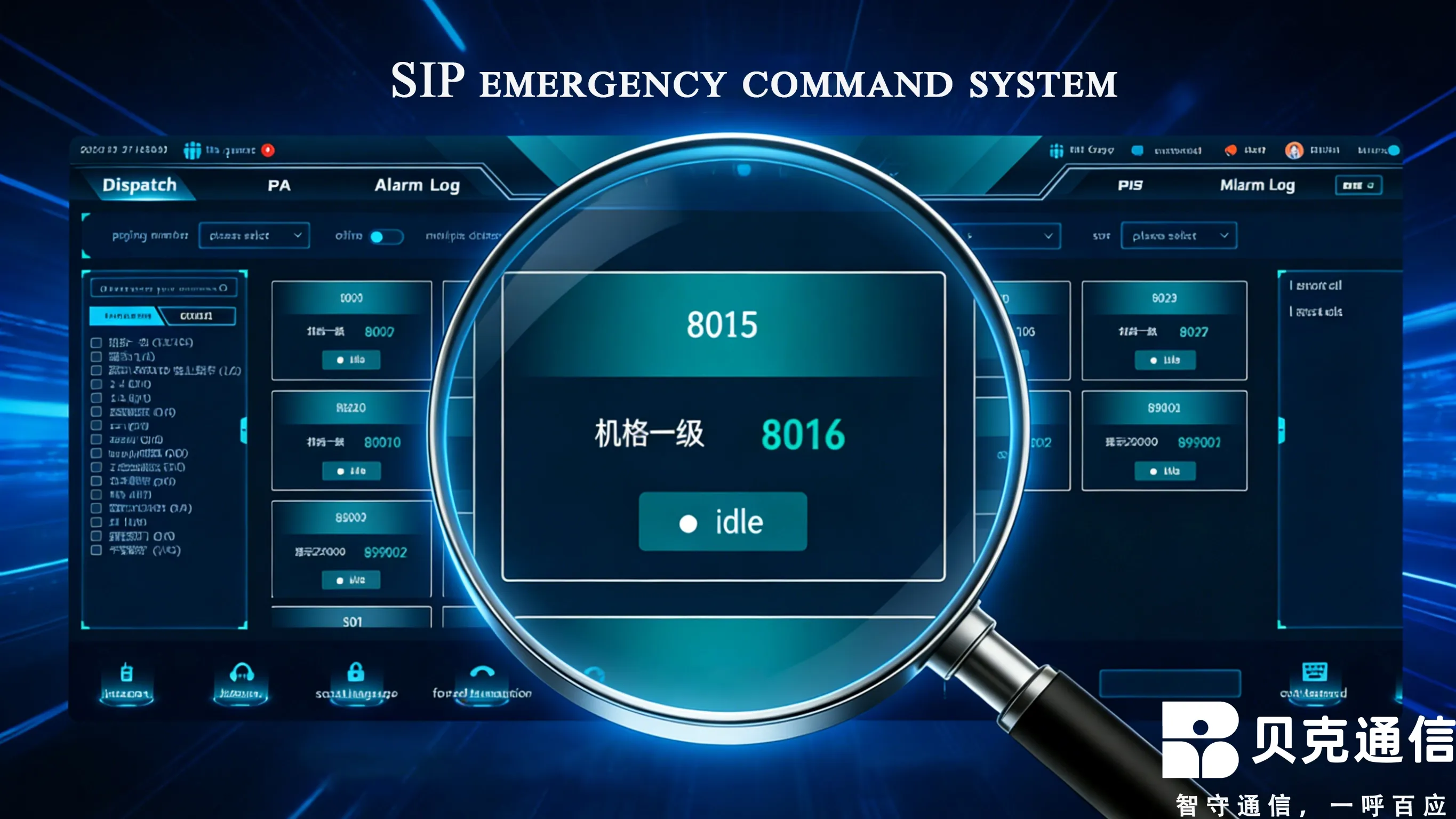
As an innovative converged communication solution, Becke Telcom SIP Paging Phone Emergency Command System has become the preferred choice for emergency communication in various scenarios. Built on Session Initiation Protocol (SIP), it deeply integrates traditional paging phones, intercom systems and IP network technology, realizing integrated voice communication, broadcast notifications and multi-party intercom. Compared with traditional independent emergency communication systems, Becke Telcom’s solution has obvious advantages: low deployment cost, high O&M efficiency, strong function linkage and flexible expansion, making it particularly suitable for scenarios with high requirements for emergency communication response speed and reliability, such as scenic spots, industrial plants and transportation hubs.
Becke Telcom Emergency Command System
Architecture Analysis of Becke Telcom SIP Paging Phone Emergency Command System
Becke Telcom SIP Paging Phone Emergency Command System adopts a three-layer architecture (core layer, transmission layer and terminal layer) to ensure stable and efficient operation. The core layer, as the control center, includes SIP servers, broadcast intercom management platforms and linkage interface modules. The SIP server supports large-capacity terminal access (up to 5,000+ units) and undertakes terminal registration, signaling processing and session control. The broadcast intercom management platform provides device management, user management, broadcast task scheduling and emergency dispatch functions, while the linkage interface module realizes interconnection with video surveillance, environmental monitoring and fire alarm systems through standardized protocols (RS485, OPC, SDK).
The transmission layer, a bridge between the core and terminal layers, consists of network switches, POE switches and transmission networks. It adopts a ring network topology based on gigabit industrial switches with self-healing function, which automatically switches data to backup paths when links fail. An independent VLAN is allocated for SIP services to avoid network congestion, and QoS technology prioritizes voice data transmission in case of congestion.
The terminal layer is the direct interaction interface with users, with devices configured according to scenario needs. In high-risk scenarios (mines, chemical industry), Becke Telcom deploys explosion-proof certified SIP terminals such as EX-BH621 explosion-proof paging phones, which maintain over 90% call clarity in 100-decibel noise. In scenic spots and parks, ordinary SIP intercom extensions and broadcast columns cover major public areas. All terminals access the core server via IP network for unified management.
The architecture follows the principles of "unified interface, high integration and low coupling". The core and transmission layers communicate via standard SIP protocol, while the transmission and terminal layers transmit media streams via RTP/RTCP protocol, simplifying deployment and maintenance and improving system reliability.
Technical Characteristics of SIP Protocol in Emergency Command Systems
SIP (Session Initiation Protocol), an application-layer control protocol formulated by IETF for multimedia sessions, is the core of Becke Telcom’s system and provides a solid foundation for emergency communication.
Its biggest advantage is fast call establishment (only 1.5 round-trip delays), much faster than the traditional H.323 protocol, which significantly shortens emergency response time. It also supports unicast, multicast and broadcast modes, meeting the diverse needs of "one-to-one calls" and "one-to-many broadcasts" in emergency command, such as simultaneous one-to-one calls between command centers and underground rescuers, and emergency broadcasts to the entire mining area.
Flexible session control is another core advantage. Through extended protocols (RFC 3581, RFC 3959), the system realizes dynamic resource allocation and priority management. Emergency calls are marked as the highest priority via the Resource-priority header field, and the Alert-Info header triggers special ringtones on terminals to attract attention.
In terms of security, SIP supports TLS encrypted signaling and SRTP encrypted media streams. The two-phase DH key exchange algorithm (128-bit key) ensures secure voice transmission with acceptable time delay, while firewall policies and NAT ALG penetration technology ensure reliable SIP signaling transmission in complex networks.
For terminal positioning and routing, the SIP protocol uses extended headers (P-Access-Network-Info) to obtain accurate terminal locations. Mine WiFi mobile terminals provide base station MAC addresses as location identifiers, and DNS NAPTR record query dynamically routes calls to the nearest call center, improving response efficiency.
Key Technologies and Implementation Steps for System Deployment
Deploying Becke Telcom’s system requires four key technologies: network planning, terminal configuration, platform construction and security strategies, which directly determine system reliability and emergency response capability.
Network planning is the foundation. In complex environments such as industrial plants, a ring topology, VLAN division and QoS strategies are recommended to ensure voice data priority. Voice transmission parameters are controlled as follows: end-to-end delay ≤ 200ms, jitter ≤ 30ms, packet loss rate ≤ 5%. POE power supply follows corresponding standards (802.3af for ordinary terminals, 802.3at/bt for high-power terminals), and IP addresses are allocated via DHCP.
Terminal configuration varies by scenario. Explosion-proof terminals must meet ATEX certification (Ex II 2G db IIB T4 Gb) and support SIP extensions. Taking Becke Telcom EX-BH621 as an example, its configuration includes password initialization, SIP server address setting, TLS certificate trust configuration and emergency call shortcut key definition. Emergency calls trigger the Alert-Info header and route to designated command centers. Terminals support multiple voice coding formats (G.711, G.729, G.722) selected based on network conditions.
Platform construction is the core. The SIP server cluster adopts active-standby mode with load balancers, and the switchover time is controlled within 6 seconds. Logical functions (proxy, redirect, registration, location servers) are separated to reduce single-node pressure. The management platform focuses on user permission management, broadcast task scheduling and real-time device status monitoring via the SUBSCRIBE/NOTIFY mechanism.
System integration realizes multi-system linkage: it connects with video surveillance via ONVIF protocol, with IoT sensors and fire alarm systems via API interfaces, and with existing business systems via SDK. For example, in chemical plants, abnormal temperature triggers intercom alarms and emergency broadcasts automatically.
Deployment Requirements and Challenges in Different Scenarios
Becke Telcom’s system faces different deployment requirements and challenges in various scenarios, requiring targeted solutions.
In scenic spots, the core challenges are complex terrain coverage and sudden large passenger flows. A hybrid network (wired + WiFi + 4G/5G) achieves full coverage. Terminal density is 1 SIP intercom terminal per 1,000-2,000 square meters and 1 emergency call terminal every 500 meters. The system supports multi-language broadcasting and uses MAC address/GPS for terminal positioning to dispatch rescue forces quickly.
In industrial plants, explosion-proof safety and environmental adaptability are key. Terminals must meet ATEX II or IECEx certification, with high-sensitivity microphones and strong noise resistance (clear calls in 100-decibel noise). PoE++ technology (802.3bt) provides long-distance, high-power power supply, and the system needs to integrate with PLC and SCADA systems, requiring high openness and compatibility.
In transportation hubs, multi-system collaboration and high concurrency processing are critical. It integrates video surveillance, security inspection and ticketing systems via standardized interfaces, and adopts dual-line redundancy and 72-hour backup power supply to ensure stability. Seamless roaming supports continuous communication for mobile terminals during area switching.
Table 1: Comparison of Deployment Parameters in Different Scenarios
Deployment Parameters | Scenic Spot Scenarios | Industrial Plant Scenarios | Transportation Hub Scenarios |
Network Topology | Hybrid Network (Wired + WiFi + 4G/5G) | Ring Topology + PoE++ Power Supply | Dual-Line Redundancy + 72-Hour Backup Power Supply |
Terminal Density | 1 unit/1000-2000㎡ | 1 unit/500-1000㎡ | 1 unit/500-800㎡ |
Voice Coding | G.711 (High Sound Quality) | G.722 (Strong Noise Resistance) | G.711 (High Definition) |
Bandwidth Requirement | 10-20Kbps/terminal | 20-30Kbps/terminal | 30-50Kbps/terminal |
Positioning Method | WiFi MAC + GPS | Base Station MAC + RFID | GPS + Base Station Positioning |
Analysis of Industry Successful Cases
Becke Telcom SIP Paging Phone Emergency Command System has been successfully applied in many industries, with the following typical cases.
Becke Telcom Mine SIP System Case: A large mine deployed Becke Telcom’s system to solve insufficient underground communication coverage and low emergency response efficiency. The system adopts a ring topology, SIP server cluster (active-standby switchover < 6 seconds), gigabit industrial switches, PoE++ power supply, and EX-BH621/EX-BH625 explosion-proof terminals. It realizes one-key emergency calls, zoned broadcasts and deep integration with GB28181 video surveillance systems. With noise suppression (90%+ clarity in 100-decibel noise), it shortens emergency response time from 8 minutes to less than 2 minutes.
Yealink Emergency Command System Case: Yealink deployed a cloud-based SIP system for Nantong Emergency Management Bureau, realizing cross-region and cross-department collaboration. It supports one-key emergency calls, real-time video conferencing, interconnection with fire and medical systems, and remote device management. With 13 security encryption protocols, it improves emergency response efficiency by over 60%.
Anhui Five-Level Emergency Command System Case: Becke Telcom’s system plays a key role in Anhui’s five-level (provincial to on-site) emergency command system. Adopting triple-network convergence (satellite, 4G/5G, fixed network), it realizes second-level response for real-time audio and video transmission and command dispatch. It has rectified 14,000 hidden dangers and improved emergency response efficiency by over 60% compared with the 13th Five-Year Plan period, performing well in the 2024 Huangshan flood and 2025 heavy rainfall disasters.
System Optimization and Future Development Trends
Becke Telcom’s system is continuously optimized with three key directions: improving stability by reducing 408/504 errors via load balancing and QoS optimization; enhancing intelligence via voice recognition and natural language processing; and improving compatibility via protocol extension and API opening (e.g., deep compatibility with GB28181 protocol).
Future trends include in-depth integration with 5G network slicing: eMBB slices for high-quality SIP broadcasts, uRLLC slices for ultra-low latency emergency calls, and mMTC slices for massive sensor access, with URSP rules realizing differentiated resource allocation.
AI integration is another key trend: voice recognition for call transcription and scheduling logs, semantic analysis for emergency keyword identification and plan triggering, and noise suppression for clear calls in complex environments (e.g., Yealink’s intelligent noise cancellation for non-voice interference).
Edge computing will improve response speed: sinking media processing to edge nodes reduces cloud latency, realizes local audio and video collection/distribution, and uses edge nodes as local data storage and analysis centers to reduce central server load.
Table 2: Future Development Trends
Development Trends | Technical Support | Application Value |
5G Network Slicing Integration | FlexE Hard Slicing, URSP Routing | Differentiated guarantees for emergency services |
In-depth AI Integration | Voice Recognition, Noise Suppression | Automatic emergency identification, improved call quality |
Edge Computing Deployment | Edge Node Media Processing | Reduced latency, improved real-time performance |
IoT Integration | Sensor Data Access, Device Monitoring | Closed-loop "perception - analysis - decision - execution" |
Deployment Implementation Steps and Precautions
Deploying Becke Telcom’s system follows six scientific steps to ensure stability and reliability.
Step 1: Demand Analysis and Planning. Clarify function requirements, coverage, terminal quantity and network environment based on scenario characteristics, and reserve interfaces for future expansion.
Step 2: Network Infrastructure Deployment. Deploy switches and transmission networks with redundancy design (ring topology, dual-line backup). Configure QoS for voice traffic, and set firewalls to allow SIP signaling (UDP/TCP 5060) and media streams (UDP 49152-53247) with NAT ALG penetration.
Step 3: Core Platform Deployment and Configuration. Deploy a SIP server cluster (active-standby, switchover ≤ 6 seconds) and configure registration, proxy and redirect servers. Set up the management platform for user permissions and broadcast templates, and enable TLS/SRTP encryption with 24-hour key rotation.
Step 4: Terminal Device Deployment and Configuration. Deploy scenario-appropriate terminals (ATEX-certified for explosion-proof environments) and configure passwords, SIP server addresses, TLS certificates and emergency shortcut keys. Add positioning functions for scenic spots via MAC address/GPS.
Step 5: System Integration and Testing. Integrate with third-party systems via API, SDK or protocol conversion, and test voice quality, emergency call priority, multi-system linkage, load capacity and redundancy switchover.
Step 6: Training and O&M. Train administrators and users, establish an O&M mechanism (regular inspections, fault diagnosis, upgrades, backups) and an emergency plan library.
Key precautions: Ensure network stability; strengthen security protection against DDoS attacks and data leakage; conduct compatibility testing; optimize user experience by simplifying operations.
Conclusions
Becke Telom SIP amplified telephone emergency command system, with its features such as rapid call establishment, flexible session control, and open scalability, is becoming an ideal choice in the field of emergency communication. Through scientific deployment and reasonable configuration, this system can significantly enhance emergency response efficiency, reduce deployment and operation costs, and provide reliable communication guarantees for various scenarios.

 English
English Deutsch
Deutsch 한국어
한국어 Русский
Русский Français
Français 日本語
日本語 لالعربية
لالعربية हिन्दी
हिन्दी Español
Español Português
Português 繁体中文
繁体中文 简体中文
简体中文